So be careful, I’m going to put out my best bad faith because this story is totally ridiculous:
- Word, Excel, PowerPoint… have the same kind of functionality (code execution) with Macros
- Outlook, which you have almost all the time open, has the same kind of functionality with Addins
- Photoshop, Illustrator… have the same kind of functionality with plugins
- Firefox, Chrome… have the same kind of functionality with plugins
So yes, KeePass can be misused and all your passwords can be recovered, but it’s been known and documented for years: https://keepass.info/help/kb/sec_issues.html#cfgw
And KeePass offers ways to make its configuration a bit more secure: https://keepass.info/help/kb/config_enf.html
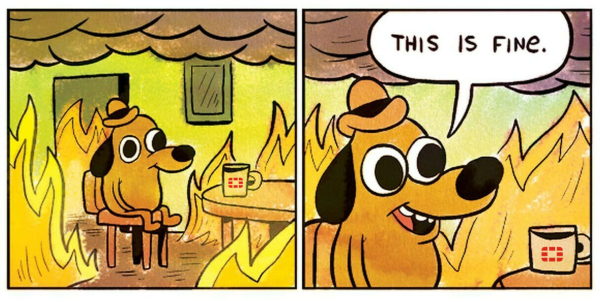
The fact remains that if an attacker has access to your computer, even with limited privileges, it is only a matter of time before he have access to everything (except possibly on a Chrome Book concerning the persistence).
Does this challenge KeePass and having a local vault?
The answer is of course: no 🤣, thank you cap’tain Obvious!
To compromise KeePass, an attacker must have access to the computer (or, in some cases, to a remote share). If an attacker has access to your computer, even with limited privileges, it’s only a matter of time before they have access to everything (except possibly on a Chrome Book for persistence).
Having a password safe is good, it’s even very good, it’s better than having a single password for all your accounts (Password Reuse my friend enemy), it’s better than having a text or excel file with your passwords…
If the password vault is used wisely, then you will have unique, long and complex passwords for each site/application, then back it up regularly.
You can also use a safe as a web application like Bitwarden self-hosted or as a pure service (SaaS) like “Bitwarden SaaS service”, LastPass, Dashlane, 1Password… (and dear reader, before you’re starting to complain about LastPass, yes, an online safe is interesting but requires a prior analysis of the threat because, indirectly, they will have your passwords cf. https://patrowl.io/third-lastpass-hack/)