Managing cyber risk effectively does not require unlimited budgets. It requires a structured, risk-based approach focused on the areas of greatest exposure.
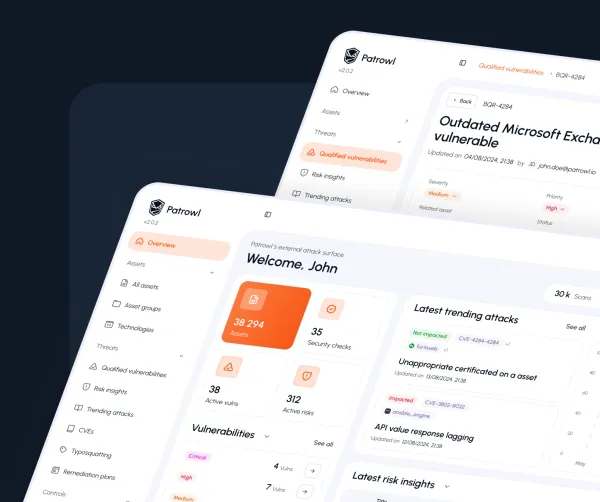
Gain Full Visibility of Internet-Facing Assets
You cannot protect what you cannot see. Many councils lack a comprehensive, up-to-date inventory of their external attack surface — the systems, subdomains, APIs, and cloud services accessible from the internet. External Attack Surface Management (EASM) tools can automate this discovery process, continuously identifying exposed assets and flagging vulnerabilities before attackers find them.
Strengthen Remote Access and Authentication
With hybrid working now standard across local government, remote access systems represent a major risk vector. Implementing multi-factor authentication (MFA) across all remote access points, enforcing strong password policies, and regularly auditing VPN and remote desktop configurations are foundational steps that significantly reduce exposure.
Manage Third-Party and Supply Chain Risk
The Locata and Synnovis attacks demonstrate that council security is only as strong as the weakest link in its supply chain. Local authorities should conduct regular security assessments of their key suppliers, require minimum security standards in procurement contracts, and have clear incident response plans for supplier-side breaches.
Apply Patches Promptly and Systematically
Unpatched vulnerabilities in internet-facing systems remain one of the most common attack vectors. Establishing a regular, prioritised patching schedule (with particular focus on externally accessible systems) closes many of the entry points that attackers rely on.
Build a Cybersecurity Culture
The NCSC has reiterated that barriers to improving cyber resilience are not purely technical but are also market- and culture-driven, calling on all leaders to take responsibility for their organisation's cyber resilience. Regular staff awareness training, clear escalation procedures for suspected incidents, and leadership commitment to cybersecurity investment are as important as any technical control.
Conclusion: From Reactive to Proactive
UK local authorities face a cybersecurity challenge that is structural, financial, and operational all at once. The combination of legacy systems, expanding digital services, limited budgets, and a rapidly worsening threat landscape creates conditions that attackers are actively exploiting.
The incidents of 2024 show that the question is no longer whether a council will face a cyberattack, but when, and how prepared it will be when it happens.
Taking a proactive approach to external attack surface management, third-party risk, and security culture is no longer optional. It is the baseline required to protect public services, safeguard citizen data, and maintain the trust that local government depends on.