Solution
Solution
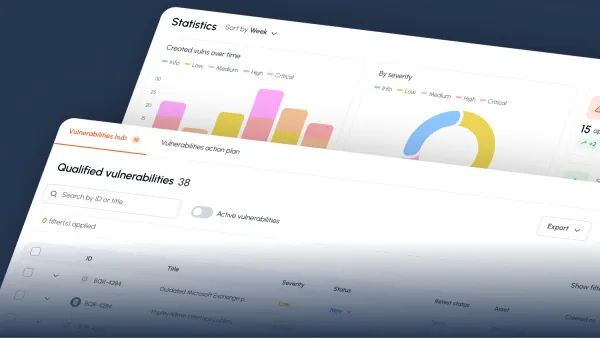
-
-
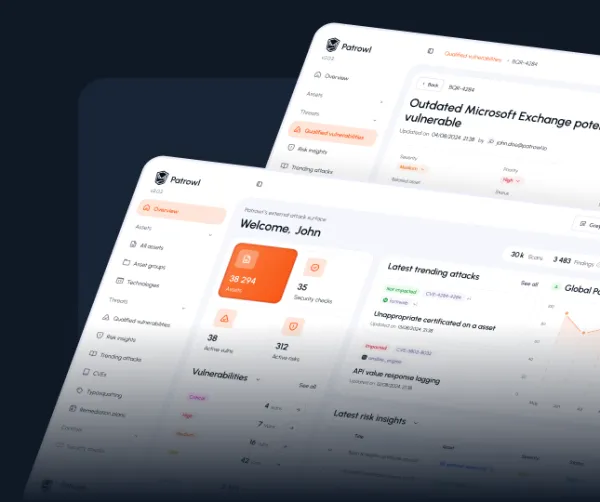
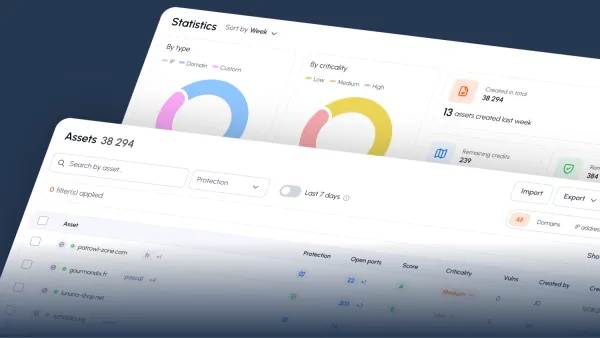
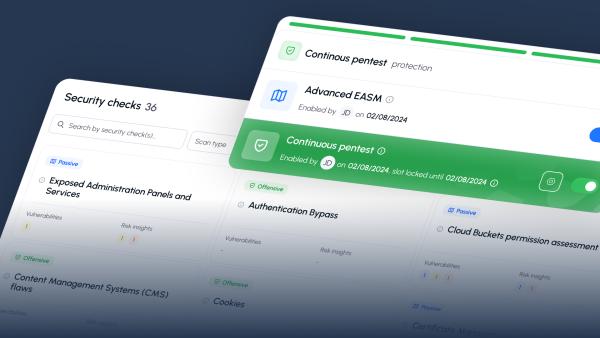
Advanced External Attack Surface Management
Discover and monitor all internet-facing assets.
-
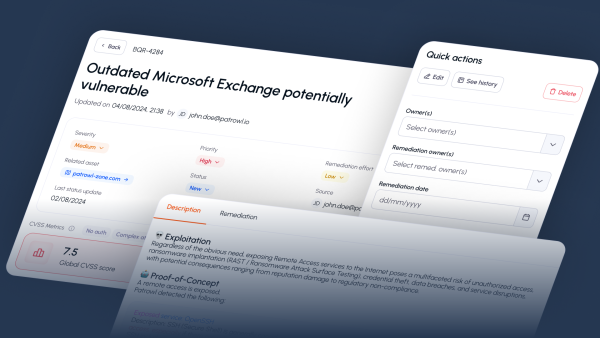
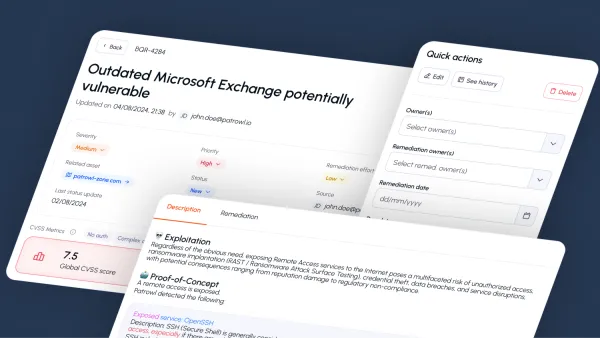
Continuous Automated Penetration Testing
Simulate real-world attacks to continuously test your defenses.